What is Passwordless Authentication and Why Is It Essential for Modern Security?
Passwordless authentication is a modern security method that enables users to access systems and applications without the need to enter a password. Instead, it relies on alternative forms of verification, such as biometric data (e.g., fingerprints or facial recognition), hardware tokens, one-time passwords (OTPs), or magic links. By eliminating passwords, this approach enhances security by reducing the risk of password theft, phishing, and weak password practices, while also offering a more seamless and user-friendly experience for users.
The reason why passwords are no longer viable is because of the plethora of applications that digital workers need to perform their jobs. Users are forced to remember or store a dizzying number of frequently changing passwords. As a result, many users resort to shortcuts like using the same password across all apps, using weak passwords or relying on risky methods like sticky notes. It becomes all too easy for bad actors to benefit from these lax practices leading to cybercrime. Compromised passwords today are a leading cause of data breaches.
Key Use Cases for Passwordless Authentication
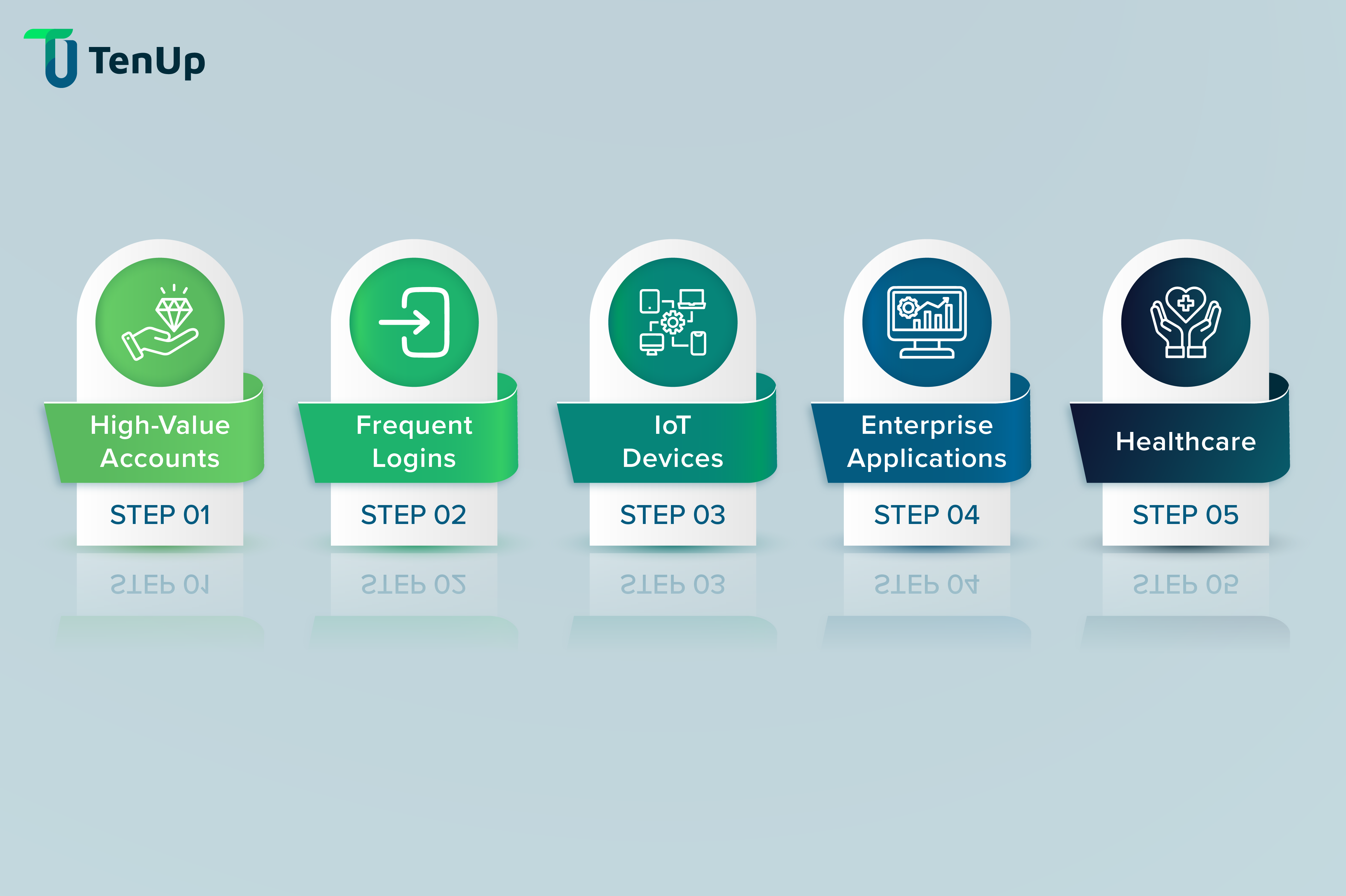
Many industries and services are especially vulnerable and at risk from attacks. Some of the most common use cases for passwordless security include:
-
High-Value Accounts
Banking, healthcare portals, and other services handling sensitive data often add passwordless as extra security.
-
Frequent Logins
Apps used daily benefit from the convenience of magic links or biometric authentication.
-
IoT Devices
Devices with limited input capabilities (smart home, wearables) can use possession-based authentication via a smartphone or smartwatch. For businesses looking to build secure and connected healthcare solutions, check out our IoT application development services for real-world implementations.
-
Enterprise Applications
At an enterprise level, passwordless authentication can streamline access to corporate resources and applications, reducing password-related support issues and improving overall security posture.
-
Healthcare
Patient confidentiality and security are paramount in healthcare. Passwordless authentication plays a vital role in enabling secure access to electronic health records, patient portals and virtual platforms.
The Rise of Passwordless Authentication: A Revolution in Cybersecurity
By eliminating the need for passwords completely, passwordless authentication aims to mitigate common security risks while enhancing user experience and convenience.
Here are some ways in which passwordless authentication can be implemented in an organisation:
-
Biometrics
Biometric authentication uses physical attributes like fingerprints, iris scan, voice recognition or facial recognition. The advantage of using this method is both ease of use and user convenience. However, it requires special hardware and there are few chances for false positives or negatives. An increasing number of devices such as mobiles, laptops and tablets now rely on biometrics to ensure user safety. Biometrics are also the preferred method of authentication for financial institutions and banking apps, offering a multi-layered security approach.
-
Hardware Token and Security Keys
Hardware tokens and security keys are physical devices that users can plug into their computers or mobile devices to verify their identity. These keys generate unique codes or digital certificates that serve as evidence of user identity. There are several types of tokens and keys:
- USB Security Keys are plugged into a device or connected via NFC to a mobile device, thus providing authentication without the need for a password.
- Similarly, hardware tokens generate codes at frequent intervals in response to user actions. The codes ensure that only users with physical possession of the token can access the account.
- Smart cards have become prominent in corporate, banking and government sectors as an additional method for passwordless authentication. They contain a chip with the user credentials, which when inserted into the reader, grant secure access to the network and systems.
-
One-Time Passwords (OTP)
One-time passwords are perhaps the most commonly used methods to bypass traditional password authentication. These are temporary codes sent to the user's registered device via SMS, email, or authenticator apps. The codes are valid for only a single use and expire within a short period, enhancing security by mitigating the risk of interception or reuse.
-
Magic links
Magic links enable users to log in to an application or a website using a one-time-use URL which is unique to them and sent to their registered email address. Every time a user wants to sign in, they key in their email address and the application creates a magic link emailed to the user. This link allows the user to log into the website and application with no additional password or authentication. Often, these links are time-sensitive and may expire after a certain period.
-
Persistent Cookies
A persistent cookie is a small piece of data stored on a device by a web browser. It can remember a user’s authentication status across multiple sessions. When users log in with biometrics or hardware tokens, persistent cookies are set to verify that the user has been authenticated. Repeat visits to the application or website then use the persistent cookie to validate and log the user in without additional steps.
-
Software Tokens
Similar to hardware tokens, software tokens are virtual representations of physical keys used for authentication. These tokens are created and stored on a user’s device and used to authenticate them during login. There are many types of software tokens including time-based one-time passwords, HMAC-based one-time passwords, or cryptography keys created with public-key algorithms.
A Step-by-Step Guide to Implementing Passwordless Authentication
There is no one-size fits-all approach to implementing passwordless authentication. Since many of these methods require a significant overhaul of your current systems, for many businesses, this means rewiring an entire system rather than switching over to a new system.
Before choosing the right approach to passwordless authentication, here’s what you need to consider:
- Security Requirements: Mission-critical applications need stronger methods like keys and tokens. User Acceptance: Any new system must be easy to use and convenient for your users to adopt it. Cost: Many passwordless authentication solutions can be expensive.
- The complexity of this exercise varies based on the architecture of your current identity and access management (IAM) systems. It is helpful to remember that any new process requires dedicated development efforts that take up extensive time and resources. Maintaining and scaling the systems after implementation is also a key consideration.
- As a result, many businesses leverage identity provider to manage their password security. These providers offer secure solutions that can scale up to millions of users easily.
Conclusion: The Future of Security in a Passwordless Authentication
Security continues to be the top concern for organisations and individuals as malicious attacks and cybercrime evolve. Passwordless authentication brings a paradigm shift to the traditional security measures, strengthening security, operations and user experience.